What is SOX Compliance?
The Sarbanes-Oxley Act of 2002 (SOX) was passed by the United States Congress to protect the public from fraudulent or erroneous practices by corporations or other business entities.
The Sarbanes-Oxley Act (SOX) defines the requirements for the integrity of source data related to financial transactions and disclosures. SOX Section 404 requires implementation of technical controls and continuous access auditing to assure the reliability of data related to financial transactions.
Goal
To protect investors by improving the accuracy and reliability of corporate disclosures made pursuant to the securities laws, and for other purposes.
What are SOX Controls?
SOX controls are measures put in place by companies for processes that impact financial reporting. The objective of SOX controls are to ensure accurate and reliable financial reporting, as well as data protection.
These controls must be applied for all business processes and cycles related to financial reporting or financial results. To be SOX compliant, companies must record, test, maintain, and regularly review controls for financial report management. Internal auditors must perform regular compliance audits to ensure controls are consistent with SOX requirements.
SOX Compliance Requirements
Following are the key compliance requirements of the SOX:
- Senior Management Responsibility: CEOs and CFOs are directly responsible for the accuracy, documentation, and submission of all financial reports to the SEC, as well as the internal control structure.
- Internal Control Report: SOX requires an internal control report that states management is responsible for an adequate internal control structure for their financial records. Any shortcomings must be reported up the chain as quickly as possible.
- Data Security Policies: SOX mandates formal data security policies, communication of those policies to all employees, and consistent ongoing enforcement. Companies should develop and implement a comprehensive data security strategy that protects and secures all financial data stored and used during normal operations.
- Proof of Compliance: SOX requires companies to maintain compliance documentation, provide them to auditors when needed, and continually perform SOX testing, monitor and measure SOX compliance objectives throughout the year.
SOX Audits
SOX compliance audits are performed once a year, by independent auditors. Before an audit occurs, the company is responsible for finding and hiring auditors and arranging all necessary meetings.
A SOX Compliance Audit is commonly performed according to an IT compliance framework such as COBIT. The most extensive part of a SOX audit is conducted under section 404, and involves the investigation of four elements of your IT environment:
- Access – physical and electronic measures that prevent unauthorized access to sensitive information. This includes securing servers and data centers, and authentication measures like passwords and lockout screens.
- Security – staff, practices, and tools deployed to prevent security breaches on devices and networks that are used for financial data.
- Change management – how the organization defines new user accounts, performs software updates, and maintains audit trails of any change to software or configuration.
- Backup – how the organization ensures any sensitive data that is lost can be restored, including data stored off company premises.
SOX Compliance Checklist
SOX compliance is imperative in protecting your data and keeping the integrity of your financial transactions intact. The best way is to follow a checklist that will help you formalise the process of achieving SOX compliance in your organization.
- Prevent Data Tempering: Implement systems that track logins and detect suspicious login attempts to systems used for financial data.
Document timelines for key activities: Implement systems that can apply timestamps to all financial or other data relevant to SOX provisions. Store such data at a remote, secure location and encrypt it to prevent tampering.
- Install Access Controls to track access: Implement systems that can receive data from practically any organisational source, including files, FTP, and databases, and track who accessed or modified the data.
- Test, verify, and disclose safeguards to auditors: Implement systems to send reports to your auditor via email — or other means of communication — on a daily basis. Grant your auditors access to these systems for them to view relevant data without actually altering anything.
- Report on effectiveness on Security Systems: Implement systems to test and validate that your security and compliance measures are effective year-round. Have systems and processes in place that collect data around breaches, security incidents, and suspicious activity.
- Detect Security Breaches: Implement systems that can identify suspicious activities on all systems relevant to SOX compliance. This system should have the ability to detect, assess, and document threats in real-time, and send detailed reports to an incident management system.
- Disclose security incidents to auditors: Implement systems that can detect and document security breaches, as well as immediately alert your SOX auditor about the incident. Enable auditors to view reports showing which security incidents occurred, which were successfully mitigated, and which were not.
Sinevis can help with SOX Compliance
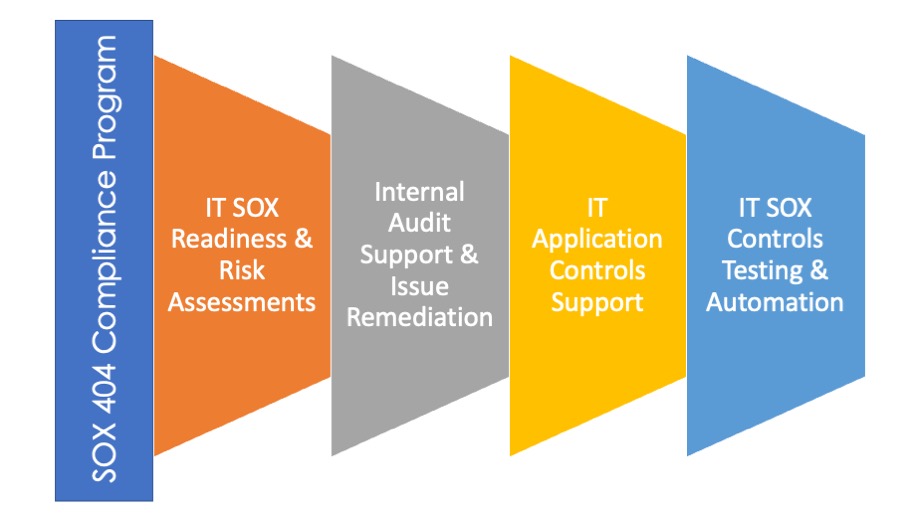
Sinevis can help an organization with the implementation and maintenance of sustainable SOX 404 compliance programs. Our team will work closely with your organisation to establish compliance programs, transfer knowledge and provide training to support a successful SOX 404 compliance program. Our team can help you with:
- IT SOX Readiness & Risk Assessments
- Internal Audit Support & Issue Remediation
- IT Application controls support
- IT SOX Controls Testing & Automation
Please contact us.